Empowering SMBs: A Resource Guide for Developing a Resilient Supply Chain Risk Management Plan
Introduction
In today’s fast-paced business landscape, small and medium-sized businesses (SMBs) play a crucial role in delivering Information and Communications Technology (ICT) products and services. To ensure the availability, integrity, and confidentiality of ICT offerings and minimize disruptions and vulnerabilities, SMBs must develop robust Supply Chain Risk Management (SCRM) plans. This resource guide, brought to you by CyberSherpas VCISO Services, is designed to empower SMBs to take charge of their SCRM efforts and meet the growing demands of private and public sector stakeholders.
The U.S. Small Business Administration defines SMBs based on industry-specific standards, typically tied to employee count or annual receipts. For the purposes of this guide, we refer to ICT SMBs as organizations with fewer than 500 employees. Recognizing that many SMBs lack dedicated risk management or SCRM expertise, this guide serves as a valuable starting point for SMBs to tailor their ICT SCRM plan.
While our primary focus is on the IT and Communications sectors, the principles discussed here are relevant to SMBs across various industries. By leveraging this resource and actively engaging in SCRM, SMBs can create actionable plans to mitigate supply chain risks, enhance resilience, and meet stakeholder procurement requirements.
Key Roles
ICT SMBs often wear different hats in the course of conducting business. To develop an effective ICT SCRM plan, it’s crucial to consider these key roles:
1. Acquirer: These are SMB owners, operators, or executives who are concerned about ICT supply chain security when making purchases.
2. Integrator: SMB integrators acquire and implement ICT products or services on behalf of their clients.
3. Supplier: These SMB owners, operators, or executives aim to win contracts where ICT supply chain security is a concern for prospective clients.

Plan Elements
Now, let’s delve into the essential plan elements that will help your SMB build a resilient SCRM strategy:
01 Begin with an Executive Summary
Your ICT SCRM plan should kick off with a concise executive summary. This should provide a high-level overview of the plan’s purpose, goals, objectives, and key elements.
02 Identify Critical Suppliers
To identify critical suppliers and assess their importance to your business, follow these steps:
- Create and maintain a list of suppliers, especially those critical to your operations.
- Identify and prioritize potential risks posed by your critical suppliers.
- Establish a formal process to refresh risk assessments and identify potential vulnerabilities in critical suppliers.
03 Identify Supply Chain Risks to Your Critical Assets
To understand which assets or suppliers may negatively impact your operations if disrupted or compromised, take these steps:
- Identify and prioritize hardware and software used in your operations.
- Establish a method for receiving patches and updates for hardware and software.
- Identify end-of-life dates for hardware and software and plan for timely transitions.
04 Implement Supplier Diversity
Reducing dependence on a single supplier can lower risks. To achieve this, consider the following:
- Develop supplier qualification criteria to ensure consistent quality.
- Build strong relationships with suppliers and maintain open communication.
- Identify single points of failure in your supply chain and have alternative suppliers ready.
05 Develop a Vendor Attestation Process
To evaluate vendors before making a purchase and maintain supplier quality over time, follow these steps:
- Establish service level agreements.
- Conduct regular audits to ensure compliance with policies and procedures.
- Monitor supplier performance regularly to meet business requirements and quality standards.
06 Develop a Contingency Plan
In the event of supply chain disruptions, including identifying alternative suppliers and backup plans, consider:
- Identifying criteria for declaring a supply chain disruption.
- Developing incident management procedures.
- Designing and documenting remediation and recovery strategies.
- Documenting lessons learned and improvement mechanisms after disruptions.
07 Train Your Employees
Ensure your employees understand the importance of managing supply chain risks and their roles in the process:
- Review existing training programs for opportunities to incorporate ICT SCRM elements.
- Develop and update employee training materials to include ICT SCRM.
- Identify key individuals who need specific ICT SCRM training.
08 Continuously Monitor and Improve
To keep your SCRM program effective and relevant, follow these steps:
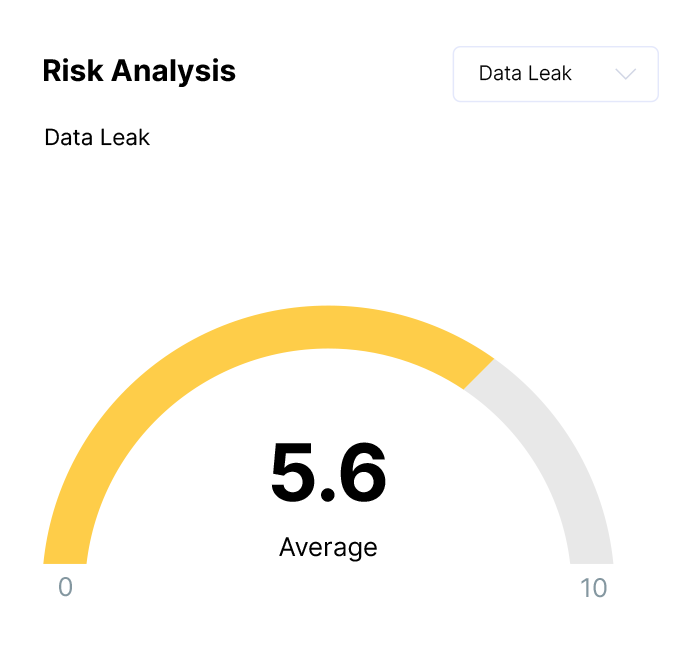
- Monitor product and service suppliers for cybersecurity incidents.
- Continuously monitor and document risks associated with suppliers.
- Reassess risks associated with suppliers routinely and as needed.
Conclusion
Developing a resilient SCRM plan is essential for ICT SMBs to thrive in a rapidly evolving business environment. By implementing the steps outlined in this resource guide and leveraging the recommended resources, you can strengthen your supply chain, mitigate risks, and build trust with stakeholders.
Remember, SCRM is an ongoing process that demands continuous attention and improvement. Stay vigilant, adapt to changing circumstances, and secure the future of your SMB in the ICT landscape.
Next Steps
For more information and access to the full list of resources, please visit CyberSherpas VCISO Services.
Now, take the first step towards securing your ICT supply chain and ensuring a resilient future for your SMB.